Update April 2025 – I have moved the PCAP files to a zip file hosted on the website so that google drive sharing permissions don’t continue to be a pain. Thanks all!
If you need to brush up on the RADIUS process, please read my previous post:
Following the 802.1X AAA process with Packet Captures
Everyone talks about it, yet I rarely meet folks that really understand what CoA (Change of Authorization) means for RADIUS authentication and client access. I recently spent a few hours troubleshooting RADIUS CoA and figure since it is fresh in my mind maybe I can share and hopefully help others out in the field.
So….
In Summary: RADIUS Change of Authorization (RFC 3576 & RFC 5176) Allows a RADIUS server to send unsolicited messages to the Network Access Server (aka Network Access Device/Authenticator in Cisco terminology e.g. AP/WLC/Switch/Firewall) to change the connected client’s authorized state. This could mean anything from disconnecting the client, to sending different attribute value pairs to the Authenticator to change the device’s VLAN/ACL and more. It is fairly robust in what it can do so I may not go too deep as I want this to be consumable.
What RADIUS CoA is NOT: Magic!
I will be walking through CoA Use Cases, what CoA looks like from a PCAP perspective, and how to gather data for troubleshooting.
RADIUS CoA Typical Use Cases:
Central captive portal (Open SSID with MAC filtering) – Especially with Cisco ISE, RADIUS CoA is the core feature set required for the captive portal. In the example below, we are redirecting a client to a splash page for either Authentication or Acceptable Use Policy review. As you can see below we have a pretty simple process.
- The client connects to the network (wired/wireless)
- Client MAC address is sent to RADIUS server as a username and password (Access-Request)
- RADIUS server responds with an Access-Accept and a URL redirect. (could also include a VLAN assignment)
- The client is redirected to the splash portal
- User logs in using the credentials required
- RADIUS server then sends a CoA with a request to reauthenticate
- Authenticator (AP/Switch/WLC) sends a CoA-ACK
- Authenticator sends an Access_Request with existing Session-Id and authentication data.
- RADIUS server then responds back with Access-Accept and any extra functions e.g. a Filter-ID for group policy assignment in Meraki Wireless.
- YAY INTERNET!
Wireless and Wired CoA-Reauthenticate Process

The above process is also used for secure device registration and URL redirects for blacklisting etc. but would involve a complete client authentication/reauthentication via EAP instead of MAC authentication. For an example check the shared captures labeled 1-of-2 and 2-of-2. These contain the EAPoL side and the RADIUS side.
Client Posturing – In some cases you may want to perform posturing on the end client. This, more often than not, requires a client on the end machine, whether it is a dissolvable agent with java, or a thick client like Cisco AnyConnect. The whole goal of posturing is making sure the clients that have access to your internal resources are properly secured from threats. A common scenario is a user removing or disabling Anti-Virus. When this event occurs it may be desired to limit that client’s access to the network until AV is reinstalled or enabled. This could be done through an ACL or VLAN change.
One of the difficult situations that arises when changing VLANs is the client may not release their IP address. In 802.11 this is easily handled by sending a disconnect-request instead of reauthentication. In wired authentication scenarios this is not typically recommended as it requires a port bounce and can take some tweaking to make work well, if at all. Instead of a VLAN change it is recommended to perform ACL changes to wired clients. On a catalyst switch this could be a dACL (Downloadable ACL) for instance.
Dynamic Network Restrictions – Closely following the use case above, a client’s access may need to be dynamically changed if they are not adhering to the network policy. Using products such as Cisco’s Stealthwatch in tandem with Cisco ISE, we could monitor a client for data dumping thresholds and change the VLAN/ACL applied to them or shut down the port to minimize the impact. This is just one example of the many possibilities.
Wireless Disconnect-Request Flow

Now on to the Fun stuff….
To capture CoA packets:
The CoA packets are only seen between the authenticator and the authentication server. Therefore we need to capture between the authenticator and the authentication server as depicted below.

In most environments this consists of using a SPAN/RSPAN port to capture traffic. Some vendors do provide the ability to perform tcpdumps/pcaps which can be a little easier, especially if you are offsite. For capture applications I tend to lean towards using wireshark as it is free and powerful. To download please go to Wireshark.org.
CoA Messages are sent on two different udp ports depending on the platform. Cisco standardizes on UDP port 1700, while the actual RFC calls out using UDP port 3799. These messages are all included in the “radius” wireshark filter.
Just in case you don’t have a test network please feel free to use the pcaps in this zip file:
RADIUS CoA Packet Types
There are two different RADIUS CoA packets that are sent from the RADIUS Server (Authentication Server):
- Disconnect-Request – Requests to terminate the session of the client.
- CoA-Request – Requests to do a number of things from reauthenticate to port-bounce, shutdown, and more.
And there are four that are sent from the NAS/NAD/Authenticator:
- Disconnect-ACK – Acknowledgment of successful disconnect
- Disconnect-NAK – Failed session disconnect
- CoA-ACK – Acknowledgment of successful CoA action
- CoA-NAK – Failed CoA action
RADIUS Server Sourced Packets
In this section we will review the two CoA messages that are sent from the RADIUS server and the useful material in the packet.
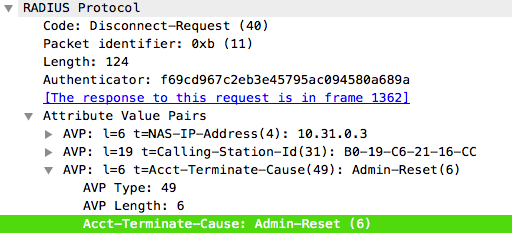
Disconnect-Request Message
Wireshark Filter: radius.code == 40
This packet is sent from the RADIUS server and is used to simply disconnect the client from the current session. This also typically involves an immediate re-authentication by the client. Disconnect-Requests can/should be used in 802.11 situations where a VLAN change needs to occur. If we simply used a CoA-Request (as we’ll see later), the client may be changed to a new VLAN while keeping the IP address it obtained from the former VLAN, clearly causing problems.

A few useful attributes in this message are:
Account-Terminate-Cause
The account terminate cause will let you know the reason for the request. This can vary but typically is classified as an Admin-Reset from a Cisco ISE Perspective.
Audit-Session-ID & Calling-Station-ID
These fields can be used to filter information from your RADIUS server regarding the client MAC address (Calling-Station-Id) and session ID. So when you need to hunt down a particular failure in a log, you can correlate the logs via these two attributes.

NAS Response Link
Wireshark helpfully gives a link to the frame that is the NAS response to the RADIUS server. This Disconnect-Ack packet will be reviewed in the authenticator sourced packets section later in this post.

CoA Request
Wireshark Filter: radius.code == 43
Unlike the Disconnect-Request above, a CoA-Request can contain a number of actions. This can include anything from reauthentication to bouncing or shutting down a port. A lot of these can be vendor specific responses. So in this instance I am going to use the Cisco ISE CoA Request info. One thing to note is useful attributes are also still the Audit-Session-Id, Calling-Station-ID, and the Response Link as well as the attributes below.

Useful Info:
Cisco-AVPair: subscriber:command = XXXXXX
This is where we are able to request that the authenticator perform a function. With Cisco ISE it is rolled into a Cisco-AVPair: subscriber:command.
For instance:
- subscriber:command=reauthenticate
This request will cause a reauthentication either for the client via EAP, or the authenticator may send the MAC address and session ID again in the event that it is a MAC authenticated session.

- subscriber:command=bounce-host-port
This is a wired only CoA Request. A request to bounce the host port will end up with a link-down link-up event on the switchport. This can be useful for trying to move a client to a new VLAN if possible. This is not something I recommend defaulting to for guest portals however as it can take some tweaking to the core CoA configurations. In ISE this would involve rewriting the Network Device Profile and CoA ReAuth requests to include a port-bounce, which I do not believe is a recommended practice.

- subscriber:command=disable-host-port
This is another wired only CoA request. This will disable the switchport if the switch supports it. I have seen cases where the end switch may not support a port shutdown and will bounce the port instead. This is not a recommended CoA request for most situations as it takes manual intervention to resolve. Instead a VLAN or ACL change is far more effective, even if the VLAN doesn’t exist (blackhole).

Authenticator Sourced Packets
Now we will review the packets that are sent in response to the CoA or disconnect request from the server. These are fairly simple and usually only include an ACK for pass or NAK for failure.
Disconnect-ACK
Wireshark Filter: radius.code == 41
This is an acknowledgment of a successful disconnect-request instruction from the authenticator to the RADIUS server. This packet can contain attributes such as the session that was disconnected, calling-station-id, or just simply the Message-Authenticator.

Disconnect-NAK
Wireshark Filter: radius.code == 42
This is an acknowledgement of a failed disconnect-request. This might happen if the client is already disconnected, or if the session has ended prior to the disconnect request. In the example screenshot we can see a bit of useful information in the error cause attribute.

CoA-ACK
Wireshark Filter: radius.code == 44
As with the Disconnect-ACK, the CoA-ACK is just an acknowledgement of the success of the CoA requested action. This packet can contain attributes such as the session that was disconnected, calling-station-id, or just simply the Message-Authenticator.

CoA-NAK
Wireshark Filter: radius.code == 45
Once again just like the Disconnect-NAK, the CoA-NAK is an acknowledgement of a failed CoA action. This could be due to lack of support or the session has ended prior to the CoA-Request. Just like the Disconnect-NAK we get a nice Error-Cause for further troubleshooting.

In closing
One thing to remember is CoA can be used to create some very complex if-this-then-that type scenarios. In the end however it is not a complex feature and definitely not magic! I hope this post was informative for you. If you find anything incorrect please let me know. Thanks and good luck!


Hi Alex, thank you for great blog about CoA. I’m building custom solution for customer and I’d like to solve CoA issue in my case (more details here: https://community.cisco.com/t5/mobility-discussions/authentication-and-coa-from-external-guest-portal/td-p/3943258). Is it possible consult my issue with you? Thanks, Martin
I apologize but I cannot assist on this ask. I do wish you luck though!
Thanks for creating this, helped me understand CoA better! You rock!
Great Content, Alex. Your blog was a trigger for me to go and take look at the RADIUS RFC. It is really interesting to see the humongous amount of data that WLC putting into these RADIUS packets when engineering a radius access request to ISE. One of the attribute in the radius also telling ISE, what is the end user’s wireless channel and his RSSI data 🙂 I have this doubt, in the case of a light weight AP, all the communications between client and WLC is packaged inside the 802.1X packet including EAP right? Or it it like the 802.1X packet only until the AP but between AP and WLC, it is radius? I thought the radius only come into picture between a WLC and ISE. With my logic, I cannot put a capture between AP and WLC to see a Radius CoA packet. The Radius happens only between WLC and ISE. So, if that’s true, why are you depicted a capture point between ap and wlc for the capturing COA?
In my diagram I am depicting a Meraki Access Point which operates as the network access device. In this case there is no WLC. If there was a WLC you’d be correct in that the communication would be between the WLC and ISE.